The move to cloud-based solutions like Office 365, Google Apps and others is one of the biggest fundamental changes IT professionals will undertake in the history of computing. Microsoft Office 365 already has >70 million paid subscriptions with a goal to have annualized revenue reach $20 BILLION by 2018.

The cost savings and productivity enhancements available to organizations are huge. But these savings and benefits can't be reaped without careful planning, network assessment, change management and continuous monitoring. Read on for things that you shouldn't do with your network in preparation for a move to one of these cloud providers.
1. Don't expect to keep the network the same as when everything was on-premise
Networks will need to change with the adoption of massive cloud-based services like Office 365. When all the traffic was on-premise, internal routers and network paths may have been burdened. Now that the traffic is largely external, it will stress the network differently and have different IT infrastructure dependencies. We call it "Service Delivery Chain."
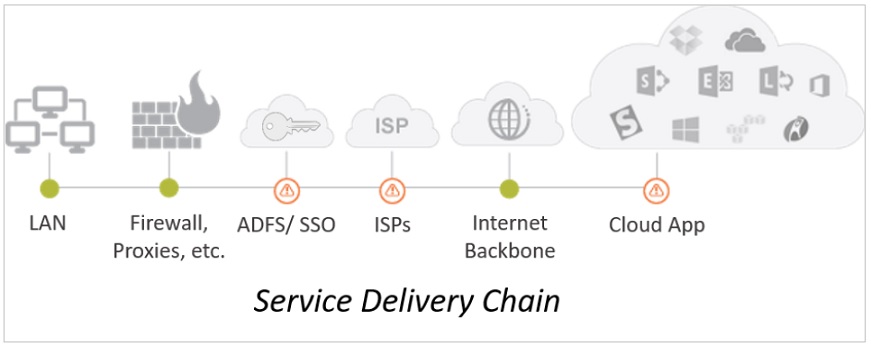
You probably thought when you adopted cloud-based services like Office 365 everything was going to be easy — just give the user a browser — but that's not the case. The Service Delivery Chain — including Single-Sign-In, Azure AD, proxies, firewalls, gateways, etc. — complicates SaaS application delivery. Especially at the branch office, for mobile and telecommuters too. End-to-end application response, uptime and availability for apps like Exchange Online, SharePoint Online and Skype for Business Online needs to be tested and measured.
2. Don't expect to keep all the firewalls and proxies just like before - they will need to change
This is a common initial desire for many mid-to-large enterprises — they want to proxy all the traffic between services such as Office 365, G-Suite and their end-users — no matter where they are. This is often seen at the beginning of migration to the cloud but it doesn't usually last or not in its initial form.
Proxying all your traffic for these services requires additional investment. It's more than likely your proxies will not be able to handle the additional load that the shift to cloud services places on them. You should synthesize and load-test the various Office 365 apps and workloads prior to and during a migration to Office 365. And you should make sure that your testing tools support proxies, single sign-on and the entire Service Delivery Chain.
3. Don't assume just because you route everything centrally, you don't need to measure end-to-end
Enterprise's may have had their own MPLS-routed networks in place for years. They put it in place back in the good old days of Exchange 2003 ;-). Then they go and believe that a decade-old network design will survive the shift to cloud/SaaS. Often, coincidental with this old network design, is their desire that they only monitor their central network because "everything just routes through to one place".
Talk about head meeting sand. If you're only monitoring from one location on the network, then you will have no idea what the experience is for end-users on the other side.
Additionally, routing everything centrally can be slow, expensive and less fault tolerant then if you sent secure, SSL-traffic directly over the Internet for branch offices and remote workers. Office 365 and wide-scale SaaS adoption for an organization places different demands on a network end-to-end.
4. Don't wait for direct data center connections like ExpressRoute for Office 365 or Azure
ExpressRoute is a new data center connection type that Microsoft has begun offering for fast connectivity from your own routed and VPN'd LAN to Office 365 and Azure tenants. Other SaaS providers often offer something similar.
Direct data center connections like ExpressRoute are still in their infancy and remain expensive. Customers still must backhaul their traffic from branch offices and other locations through their private WAN, into and out of the ExpressRoute colocation. While it sounds like it could make things simpler and faster, it does make the Service Delivery Chain longer and more complex where lots could go wrong that affects end-user experience.
5. Don't assume the problem is just going to be with the provider
The assumption that only providers like Microsoft, Google or Amazon are going to have problems is NOT a good way to start an organization's journey to wide-scale adoption of cloud services. You will have outages along the way and even post migration. The outages will occur within your own networks, your ISPs, your proxies, your Single Sign-On providers — everywhere. But with the right end-to-end monitoring and management you'll be able to quantify them and their consequences and hold each of the parties accountable for the Service Level Agreements they are signing up for.
The Latest
A vast majority (89%) of organizations have rapidly expanded their technology in the past few years and three quarters (76%) say it's brought with it increased "chaos" that they have to manage, according to Situation Report 2024: Managing Technology Chaos from Software AG ...
In 2024 the number one challenge facing IT teams is a lack of skilled workers, and many are turning to automation as an answer, according to IT Trends: 2024 Industry Report ...
Organizations are continuing to embrace multicloud environments and cloud-native architectures to enable rapid transformation and deliver secure innovation. However, despite the speed, scale, and agility enabled by these modern cloud ecosystems, organizations are struggling to manage the explosion of data they create, according to The state of observability 2024: Overcoming complexity through AI-driven analytics and automation strategies, a report from Dynatrace ...
Organizations recognize the value of observability, but only 10% of them are actually practicing full observability of their applications and infrastructure. This is among the key findings from the recently completed Logz.io 2024 Observability Pulse Survey and Report ...
Businesses must adopt a comprehensive Internet Performance Monitoring (IPM) strategy, says Enterprise Management Associates (EMA), a leading IT analyst research firm. This strategy is crucial to bridge the significant observability gap within today's complex IT infrastructures. The recommendation is particularly timely, given that 99% of enterprises are expanding their use of the Internet as a primary connectivity conduit while facing challenges due to the inefficiency of multiple, disjointed monitoring tools, according to Modern Enterprises Must Boost Observability with Internet Performance Monitoring, a new report from EMA and Catchpoint ...
Choosing the right approach is critical with cloud monitoring in hybrid environments. Otherwise, you may drive up costs with features you don’t need and risk diminishing the visibility of your on-premises IT ...
Consumers ranked the marketing strategies and missteps that most significantly impact brand trust, which 73% say is their biggest motivator to share first-party data, according to The Rules of the Marketing Game, a 2023 report from Pantheon ...
Digital experience monitoring is the practice of monitoring and analyzing the complete digital user journey of your applications, websites, APIs, and other digital services. It involves tracking the performance of your web application from the perspective of the end user, providing detailed insights on user experience, app performance, and customer satisfaction ...






